The SmallStep client installation on Windows can be done in different ways depending on the environment you want to use to work and activate connections to the machines:
- using package manager scoop on PowerShell
- using Windows Subsystem for Linux (WSL) with a Linux distribution installed from Microsoft Store
Warning: The Putty shell does not support the 2FA system provided by Cineca.
Windows PowerShell
Open the PowerShell, and the window as shown below appears
Then type the following commands in the PowerShell window:
- Download and install scoop
- Test scoop:
- Install git support for scoop
- Install smallstep
- Verify smallstep
Configuration of the step client
Initialize the client with the command:
step ca bootstrap --ca-url=https://sshproxy.hpc.cineca.it --fingerprint 2ae1543202304d3f434bdc1a2c92eff2cd2b02110206ef06317e70c1c1735ecd
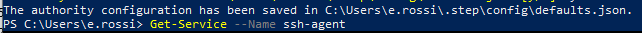
If everything is fine the following messagg will compare on the shell:
Activation of the ssh-agent
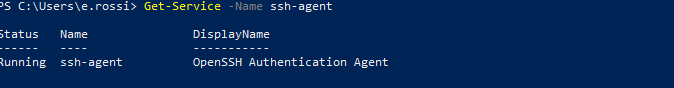
On the system windows 10/11 the ssh-agent is active by default. You can verify it with the command:
Get-Service -Name ssh-agent
and the output on the PowerShell will be:
If the service is not in "running status" it can be activated with:
Start-Service -Name ssh-agent
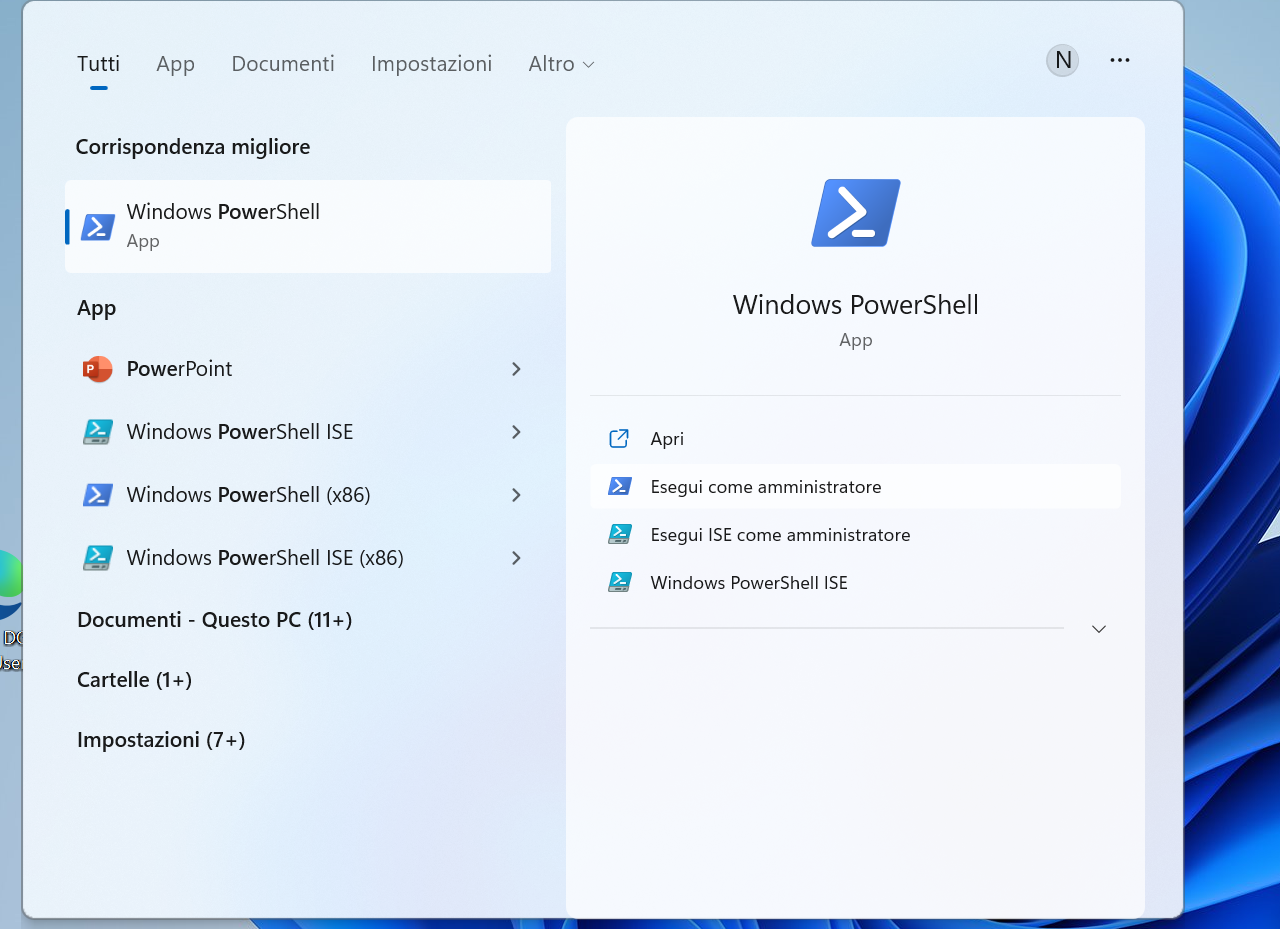
If is still not working , it is necessary to open the PowerShell as admin:
and execute the following commands:
$ Set-Service -Name ssh-agent -StartupType Auto
$ Start-Service ssh-agent
Subsequent use
Run the following command to get the timed certificate:
step ssh login <your-email> --provisioner cineca-hpc
Enter your HPC credentials in the web interface window/tab that opened.
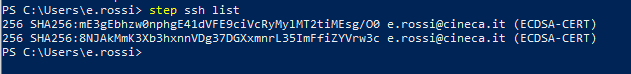
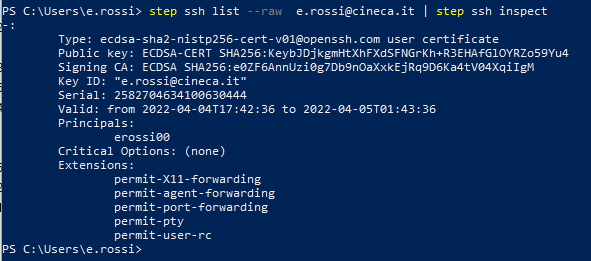
To view the issued certificate and its validity status:
step ssh list
step ssh list --raw 'email@cineca.it' | step ssh inspect step
Now you can login to the cluster.
Windows Subsystem Linux (WSL)
It is necessary to open a shell and install step following exactly the installation instructions for the linux environment.
Please note that WSL doesn't support separate tabs, and if you open a new window, this by default doesn't see the step certificate already issued from the previous tab. To avoid creating a new timed certificate for each session, we suggest to implement in your .bashrc an automatic verification of the created certificate based on the variables initialized by the "eval $(ssh-agent)" command, that can be redirected in an appropriate text file. For example:
if [ -f ~/.bash_agent ]; then
. ~/.bash_agent
fi
steptest=$(step ssh list --raw '<user-email>'| step ssh inspect | grep "Valid")
if [ -z "$steptest" ]
then
eval $(ssh-agent)
echo "export SSH_AUTH_SOCK=$SSH_AUTH_SOCK" > ~/.bash_agent
echo "export SSH_AGENT_PID=$SSH_AGENT_PID" >> ~/.bash_agent
step ssh login '<user-email>' --provisioner cineca-hpc
fi