Configuration of the step client
To initialize the client on your Linux system, you should run the following command in your local shell:
$ step ca bootstrap --ca-url=https://sshproxy.hpc.cineca.it --fingerprint 2ae1543202304d3f434bdc1a2c92eff2cd2b02110206ef06317e70c1c1735ecd
The root certificate has been saved in <path-to>/.step/certs/root_ca.crt.
The authority configuration has been saved in <path-to>/.step/config/defaults.json.
ATTENTION: if you have a previous version of smallstep installed and configured on your system, the client will ask if you want to overwrite the existing configuration. To save a copy of a previous version of smallstep installed and configured on your system, make a copy of the directory .step.
Activation of the ssh-agent
To use the certificate, the user should activate the ssh-agent running:
$ eval $(ssh-agent)
At this point, to obtain the certificate run:
$ step ssh login '<user-email>' --provisioner cineca-hpc
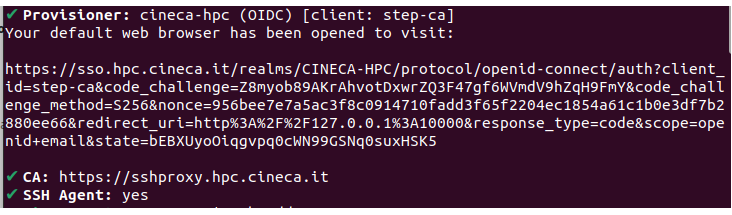
the command will report on the shell an output like the following one:
Once you have obtained the certificate, the following page on keycloack will open automatically on the browser. The user has to put his/her cluster credentials (username and password) and push the button "Sign in". Then, the keycloak will ask for the OTP code generated by the Authenticator ( see Configure the OTP ).
It is possible to check the own certificate both via ssh-agent and the step command as follow:
$ ssh-add -L
ecdsa-sha2-nistp256-cert-v01@openssh.com AAAAKGVjZHNhLXNoYTItbmlzdHAyNTYtY2VydC12MDFAb3BlbnNzaC5jb20AAAAgYjJfSnpeTTNrMHB4Lm9yX3YjZWNxXyRxcHM9blRzU1gAAAAIbmlzdHAyNTYAAABBBAJRZ11/PIo0VJknlFMDa5BIaJp/w0OWd95ueZbWlQ4uG92aSZ+K8aKgkyDiOGla3x7l+saVT/pIR+x3zBgvwgkLrbmYufPPVAAAAA
EAAAAUbS5tb3Jnb3R0aUBjaW5lY2EuaXQAAAAMAAAACG1tb3Jnb3R0AAAAAGILhpwAAAAAYgv3HAAAAAAAAACCAAAAFXBlcm1pdC1YMTEtZm9yd2FyZGluZwAAAAAAAAAXcGVybWl0LWFnZW50LWZvcndhcmRpbmcAAAAAAAAAFnBlcm1pdC1wb3J0LWZvcndhcmRpbmcAAAAAAAAACnBlcm1pdC1wdHkAAAAAAAAADnBlcm1pdC11c2VyLXJjAAAAAAAAAAAAAABoA
AAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBAE3K7f5piMLWXDm9c6kd+VAJmBClKXkQ9i/8E1UA9DcBFofX+r9JyBOULZSDkGtr84oqpNX0fa5DMCar3AQp1YAAABkAAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAABJAAAAIDg33ohPQ6BgzV1ATGsSVSbRwrbYa8LprV2EEHk4mMgWAAAAIQCkd8QKYS+zbeyD1nXeuRAXVWJXJeoxMScgDVx2
qqu2Mg== <user-email>
$ step ssh list
256 SHA256:x+QEW8xmDBtRjVRtAukc7v7zKEHef/9joyFP9n/gZtk <user_email> (ECDSA-CERT)
To examine the validity of the certificate run:
$ step ssh list --raw '<user_email>| step ssh inspect
-:
Type: ecdsa-sha2-nistp256-cert-v01@openssh.com user certificate
Public key: ECDSA-CERT SHA256:TdhIpD5KFZD37roGYcDstS7180TruOnNgNJeS8eJJPk
Signing CA: ECDSA SHA256:e0ZF6AnnUzi0g7Db9nOaXxkEjRq9D6Ka4tV04XqiIgM
Key ID: "<user_email>"
Serial: 841532770994081620
Valid: from 2022-02-15T11:55:24 to 2022-02-15T19:55:24
Principals:
<username>
Critical Options: (none)
Extensions:
permit-X11-forwarding
permit-agent-forwarding
permit-port-forwarding
permit-pty
permit-user-rc